wLCG Grid Certificates
Background
After many many years, the German GridKa Certification Authority (CA) at KIT in Karlsruhe will cease operation at 11 June 2023 as the CA cert ends. As a successor the GÉANT Europe’s leading collaboration on network and related infrastructure and services for the benefit of research and education offers the service “HARICA Certificate Manager” to obtain Grid user certificates starting now. In addition, we also offer certificates issued by the DFN (Deutsches Forschungsnetz).
Introduction
On order to access global Grid resources, users must hold a valid personal Grid user certificate (authentication) AND users must be member of a Virtual Organization (VO) (authorization). A valid Grid user certificate is a prerequisite to request membership in a VO. Users usually have one Grid user certificate. Multiple VO membership is possible.1
A Grid user certificate (format X509) consists of a private key with a private password and a certified public key. The private key and the password is exclusively possessed by the user and is NOT known to the Registration Authority (RA) or Certification Authority (CA) at any stage.
A certificate is valid for one (1) year and can be renewed. Users get notified by the CA via email three (3) weeks before the expiration date. It is strongly recommended to renew the certificate before its expiration.
The certificate can/should be copied to all devices/browsers which need it.
Authorities
The GÉANT CA is part of The International Grid Trust Federation (IGTF) hence Grid user certificates are accepted by all Grid sites in WLCG. In order to facilitate the request procedure, many institutions in Germany operated Registration Authorities (RA) which take over the necessary paper-work on behalf of the CA.
The procedure you need to follow to optain a certificate depends on the CA you want to use: HARICA or DFN. HARICA will allow you - once authorized - to get and renew your certificate solely based on your ZIM login. DFN is a more manual process, but has proven to work under all circumstaces.
Procedure for HARICA
- Send you ZIM login name (not the password of course!) to the PLEIADES team (using the normal support email. Wait for a confirmation that your ZIM account was included in the lists of accounts who can generate a Grid certificate. You only have to do it once - the registration will be good for upcoming renewals of your certificate.
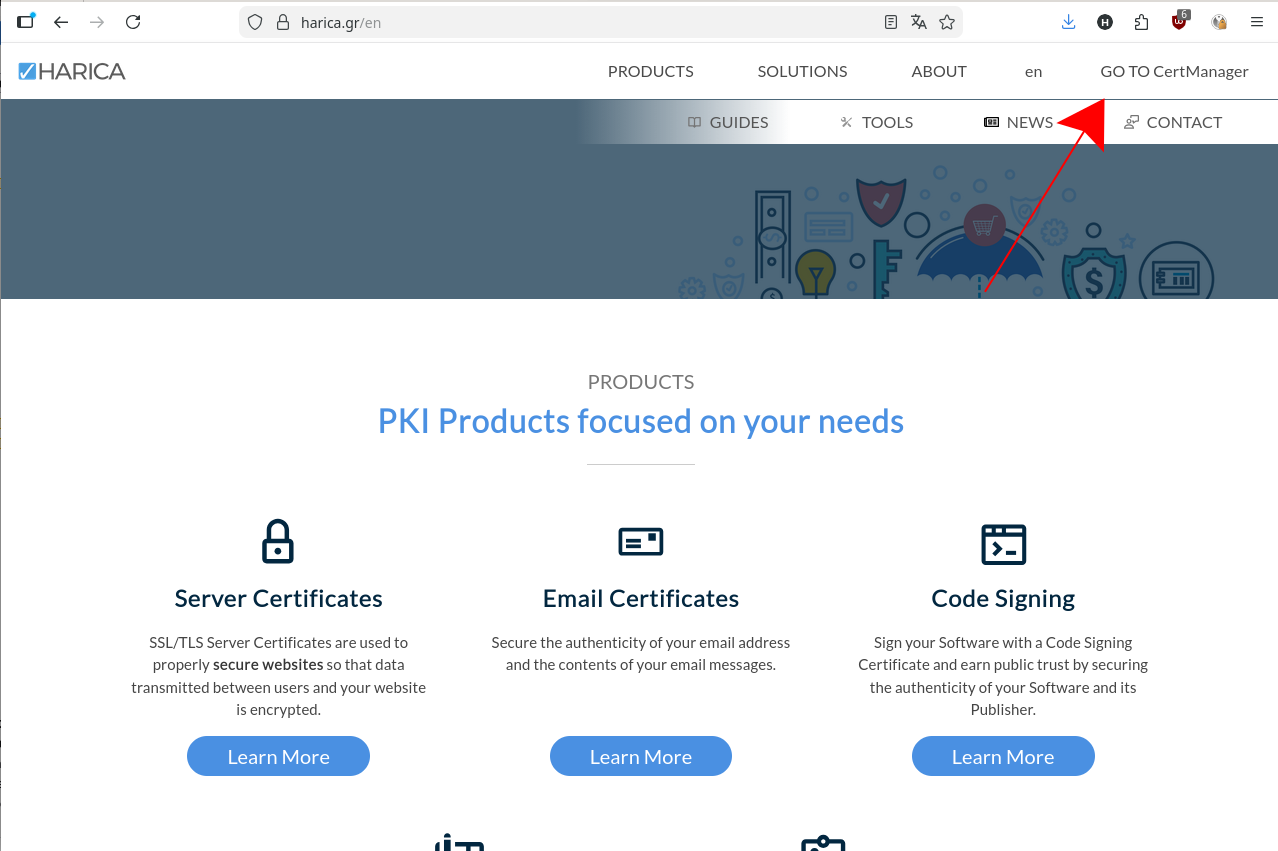
- Visit the HARICA Homepage, click on “GO TO CertManager”:
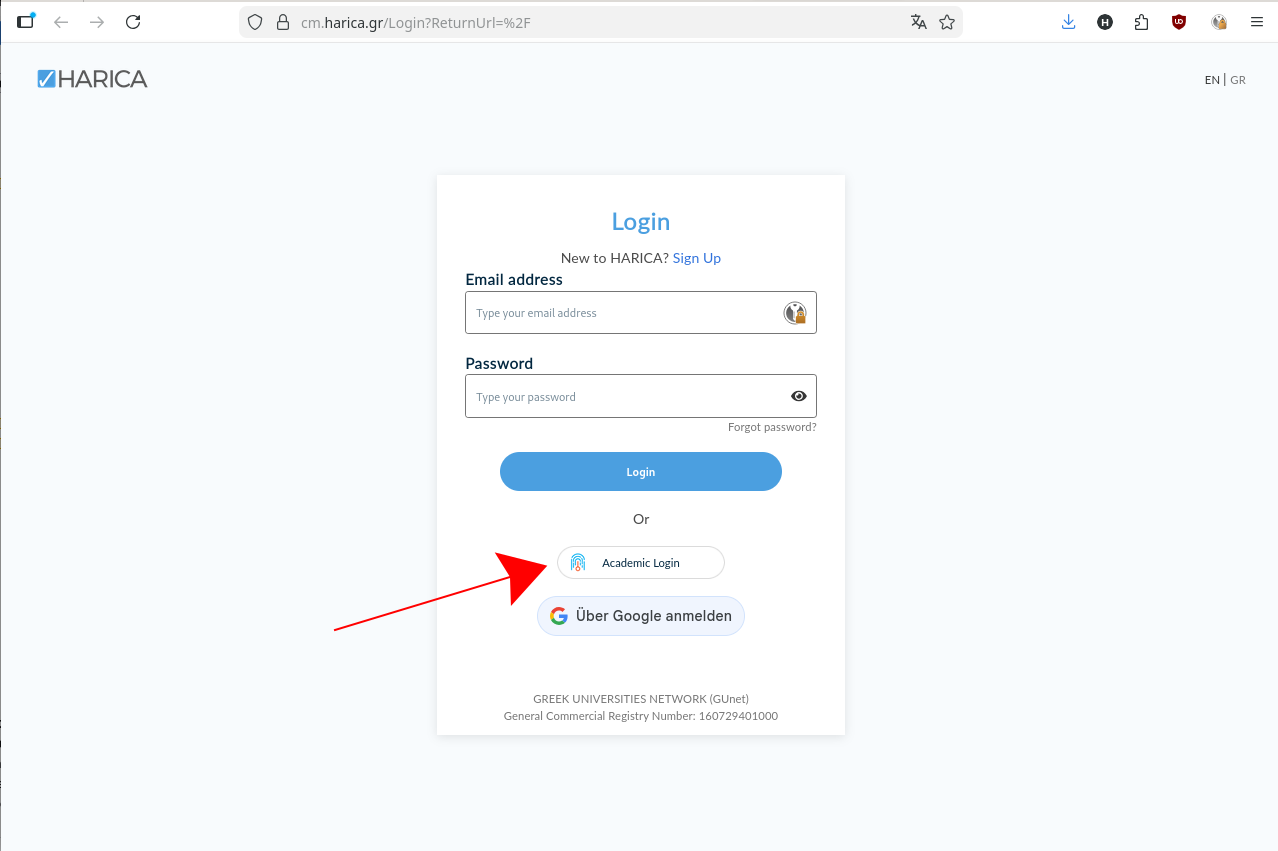
- Select “Academic Login”:
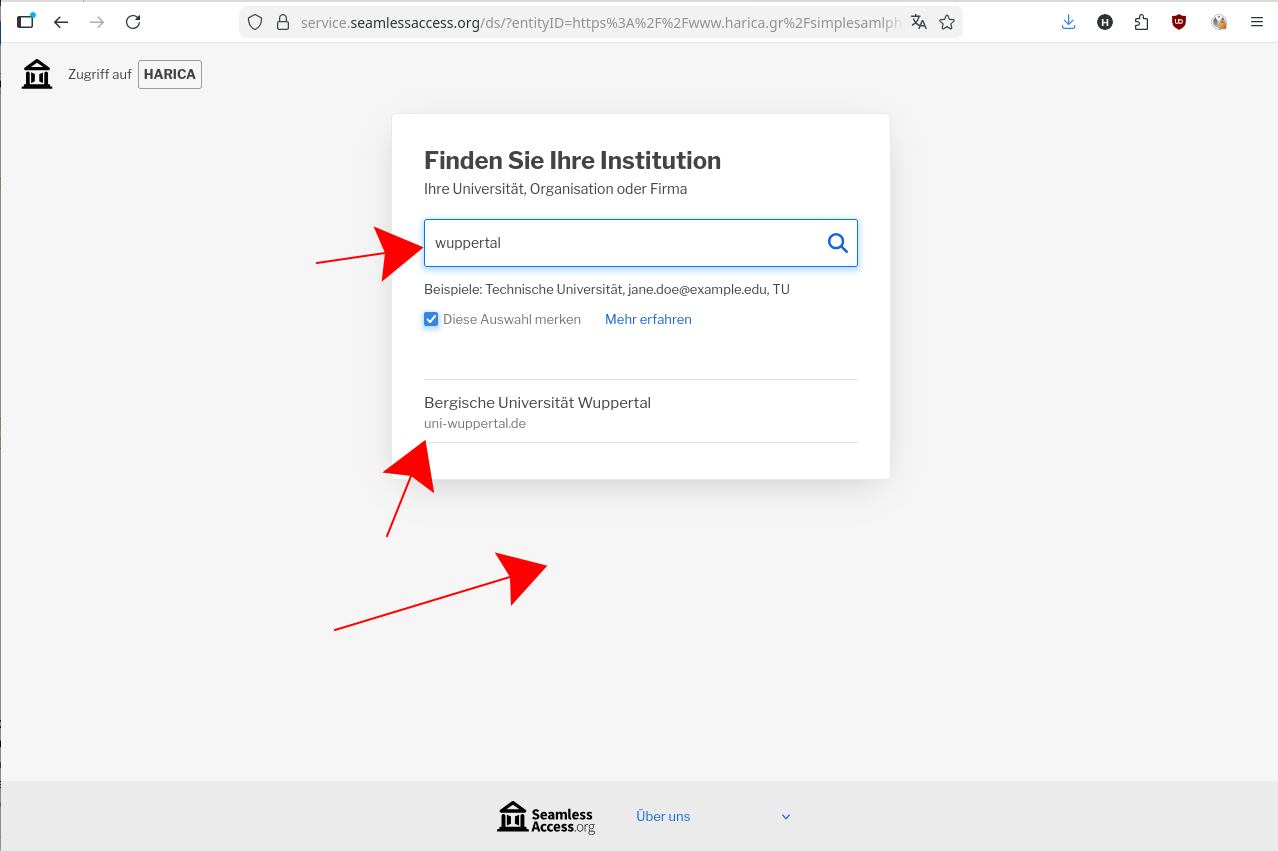
- Search for Wuppertal, select “Bergische Universität Wuppertal”:
- On the following page, select on the left column “IGTF Client Auth”, then select “GÉANT Personal Authentication”:
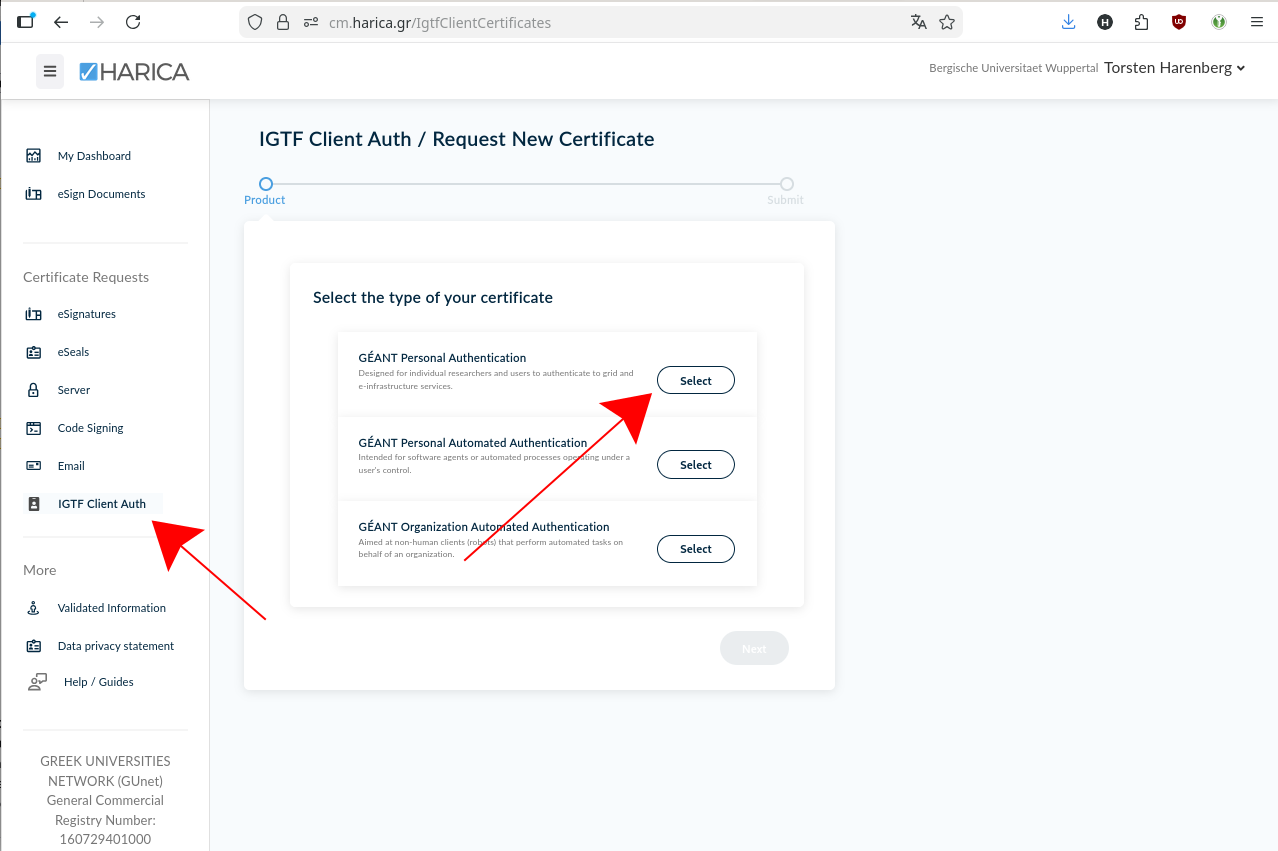
If you do not see the “IGTF Client Auth” on the left hand side, your ZIM account is not correctly authorized. Contact the PLEIADES crew. - On the following screen, your name and email are already filled in, just agree on the terms and click “submit request”:
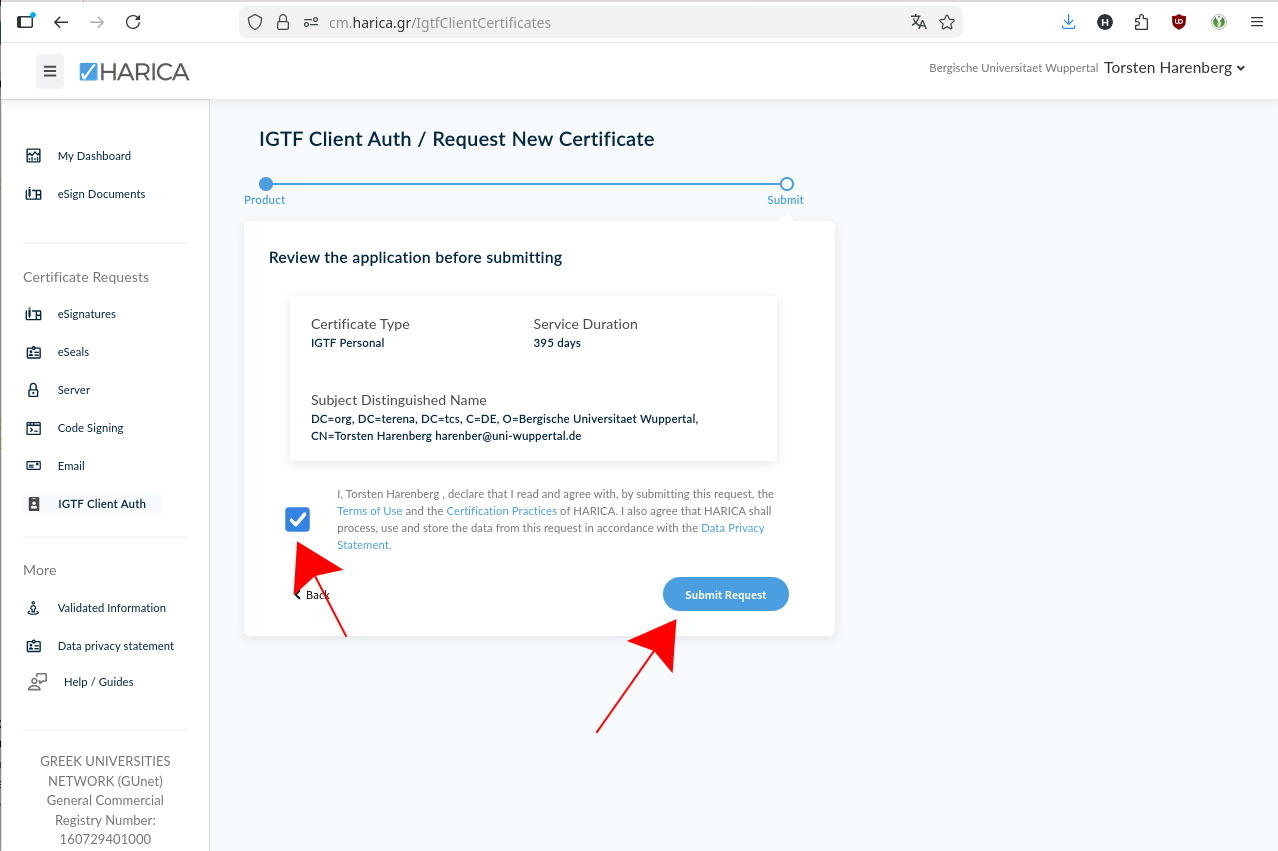
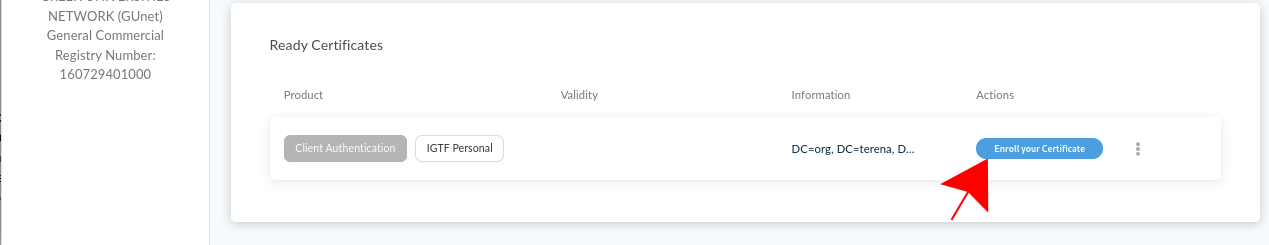
- You should see your certificate under “Ready Certificate” after a few seconds. Click on “Enroll your Certificate”:
- On the last page, you download your certificate. you can only do that once!. Ensure that “Generate Certificate” is selected on top, enter a passphrase twice do not forget this! We highly recommend to use a password manager to ensure that you already remember your chosen passphrase. Tick the text on the button and finally click on “Enroll Certificate”, which will download your new Grid certificate as
Certificate.p12file. Store it at a safe place. - continue with the Common procedures below
Procedure for DFN
- Request a “Nutzerzertifikat”/”User certificate” at the DFN PKI page for Wuppertal. Keep the “Antragsdatei” (a json file) in a safe place and do not loose it. It contains your certificate key, which cannot be recovered if this file gets lost.
- With the printed form, visit Torsten Harenberg together with a piece of government ID (national ID card or passport)
- after a short while, you will receive an email with instructions how to download the new certificate. You will need the “Antragsdatei” generated in step 1 for that.
- continue with the Common procedures below
Common procedures
- on Linux machines with Grid setups, the certificate and key files are usually placed in the directory ~/.globus/
- Download the
certs.p12file the User Cert Manager offers you. - copy it to
~/.globus/certs.p12 - Extract a certificate from it with
openssl pkcs12 -clcerts -nokeys -in certs.p12 -out usercert.pem- the certificate is your passport, you “show” to services to authenticate yourself
- Extract a key from it with
openssl pkcs12 -nocerts -in certs.p12 -out userkey.pem. - Make sure the key can only be read by yourself:
chmod 400 userkey.pem.- the key file is your secret key, that unlocks your certificate. Protect the key with a good password, do not share the key with anyone and backup the key, as it cannot be recovered, if the file got lost or you forgot the password
- in addition import the certs.p12 into your browser:
- Firefox: Settings → Certificates → View Certificates → Your Certificates → Import
- Chrome: Settings → Security → Manage Certificates → Import (depends on your operating system, that’s why we stongly recommend Firefox!)
- Download the
- with your user certificate as “passport” you have to register at your experiment/VO - so that your experiment/VO accepts your certificate and you can use experiment resources.
- if you have already registered a (previous) certificate, you can add another certificate DN (DN= text string in your certificate, that identifies you) to your experiment account
- for ATLAS, this IAM server is the central point for your registration
- more information about Grid Certificate and VO Membership from an ATLAS point of view is available here
- Depending on your browser version, it might be necessary to check in your browser’s certificate trust settings → the
The USERTRUST Networkcertificate authority needs to be trusted for all operations- Firefox:
- Settings → Certificates → View Certificates → Authorities in the
The USERTRUST Networkblock, selectEdit Trustif forGEANT eScience Personal CAand ensure, that all trust settings are enabled
- Settings → Certificates → View Certificates → Authorities in the
- Chrome:
- Settings → Security → Manage Certificates → Authorities search for
org-The USERTRUST Networkand ensure, that for both entries under⋮→ Edit all trust settings are selected
- Settings → Security → Manage Certificates → Authorities search for
- Firefox:
- to avoid problems with previous certificates, restart your browser after importing and backing up the certificate and key has been done. I.e., to quit Firefox or Chrome explicitly select
QuitorExit, respectively, from the browsers’ menues.- if everything works with your new certificate, you can optionally delete your previous certificate
Technicalities
Technically a new private/public key pair is created with every renewal.
Finding certificates in Firefox browser
Preferences -> Privacy & Security -> Certificates -> View Certificates -> Your Certificates (-> Backup)
Extracting the cert Files
Download/export the file either form the browser or directly to the ~/.globus/usercert.p12 directory and make sure to safe the old files. Then use openssl to extract ~/.globus/usercert.pem and ~/.globus/userkey.pem. Have your export passphrase at hand!
cd ~/.globus
> mv certs.p12 certs.p12.old
> mv usercert.pem usercert.pem.old
> mv userkey.pem userkey.pem.old
> ls -l
-r-------- 1 account group 8213 24. Jan 14:36 certs.p12
-r-------- 1 account group 2611 31. Jan 13:40 certs.p12.old
> openssl pkcs12 -clcerts -nokeys -in certs.p12 -out usercert.pem
> openssl pkcs12 -nocerts -in certs.p12 -out userkey.pem
> ls -l
-r-------- 1 account group 8213 24. Jan 14:36 certs.p12
-r-------- 1 account group 8213 24. Jan 14:38 usercert.pem
-r-------- 1 account group 2611 31. Jan 13:42 userkey.pem
Inspecting Grid user certificates
Please make sure your public (usercert.pem) and private (userkey.pem) keys are:
- in the correct directory,
- have the correct permissions,
- show your DN,
- are valid,
- match each other (have the same md5sum),
- you remember the password.
> cd ~/.globus
> ls -l
...
-r--r--r-- 1 account group 1728 8. Apr 09:36 usercert.pem
-r-------- 1 account group 2012 8. Apr 09:36 userkey.pem
> openssl x509 -subject -issuer -dates -noout -in usercert.pem
subject= /DC=org/DC=terena/DC=tcs/C=DE/O=Bergische Universitaet Wuppertal/CN=Harenberg, Torsten harenber@uni-wuppertal.de
issuer= /C=NL/O=GEANT Vereniging/CN=GEANT eScience Personal CA 4
notBefore=Apr 20 00:00:00 2022 GMT
notAfter=Apr 20 23:59:59 2023 GMT
> openssl x509 -noout -modulus -in usercert.pem | openssl md5
> openssl rsa -noout -modulus -in userkey.pem | openssl md5
-
A Grid user certificate can be seen as an analogy to a passport, whereas the VO membership compares to a visa. ↩